- What Are Church Fraud Detection Systems?
- Assessing Your Church Fraud Risk
- Core Features Every Admin Needs
- Implementing Detection Technology
- Manual Controls That Prevent Loss
- Monitoring Digital Giving Securely
- Auditing And Reconciliation Routines
- Investigating Suspected Misconduct
- Response Playbook And Templates
- Metrics To Track And Report
- Comparing Detection Approaches
- Practical Guide For Small Churches
- Building A Prevention Culture
- Common Implementation Mistakes
-
FAQs
- How Do Church Fraud Detection Systems Work?
- What Are The Red Flags Of Embezzlement?
- Can A Small Church Afford Detection Tools?
- When Should We Call Law Enforcement?
- What Metrics Show Detection Effectiveness?
- Which Systems Integrate With My ChMS?
- How Long Does Investigation Usually Take?
- Does Insurance Cover Employee Theft?
- What Are Church Fraud Detection Systems?
- Assessing Your Church Fraud Risk
- Core Features Every Admin Needs
- Implementing Detection Technology
- Manual Controls That Prevent Loss
- Monitoring Digital Giving Securely
- Auditing And Reconciliation Routines
- Investigating Suspected Misconduct
- Response Playbook And Templates
- Metrics To Track And Report
- Comparing Detection Approaches
- Practical Guide For Small Churches
- Building A Prevention Culture
- Common Implementation Mistakes
-
FAQs
- How Do Church Fraud Detection Systems Work?
- What Are The Red Flags Of Embezzlement?
- Can A Small Church Afford Detection Tools?
- When Should We Call Law Enforcement?
- What Metrics Show Detection Effectiveness?
- Which Systems Integrate With My ChMS?
- How Long Does Investigation Usually Take?
- Does Insurance Cover Employee Theft?
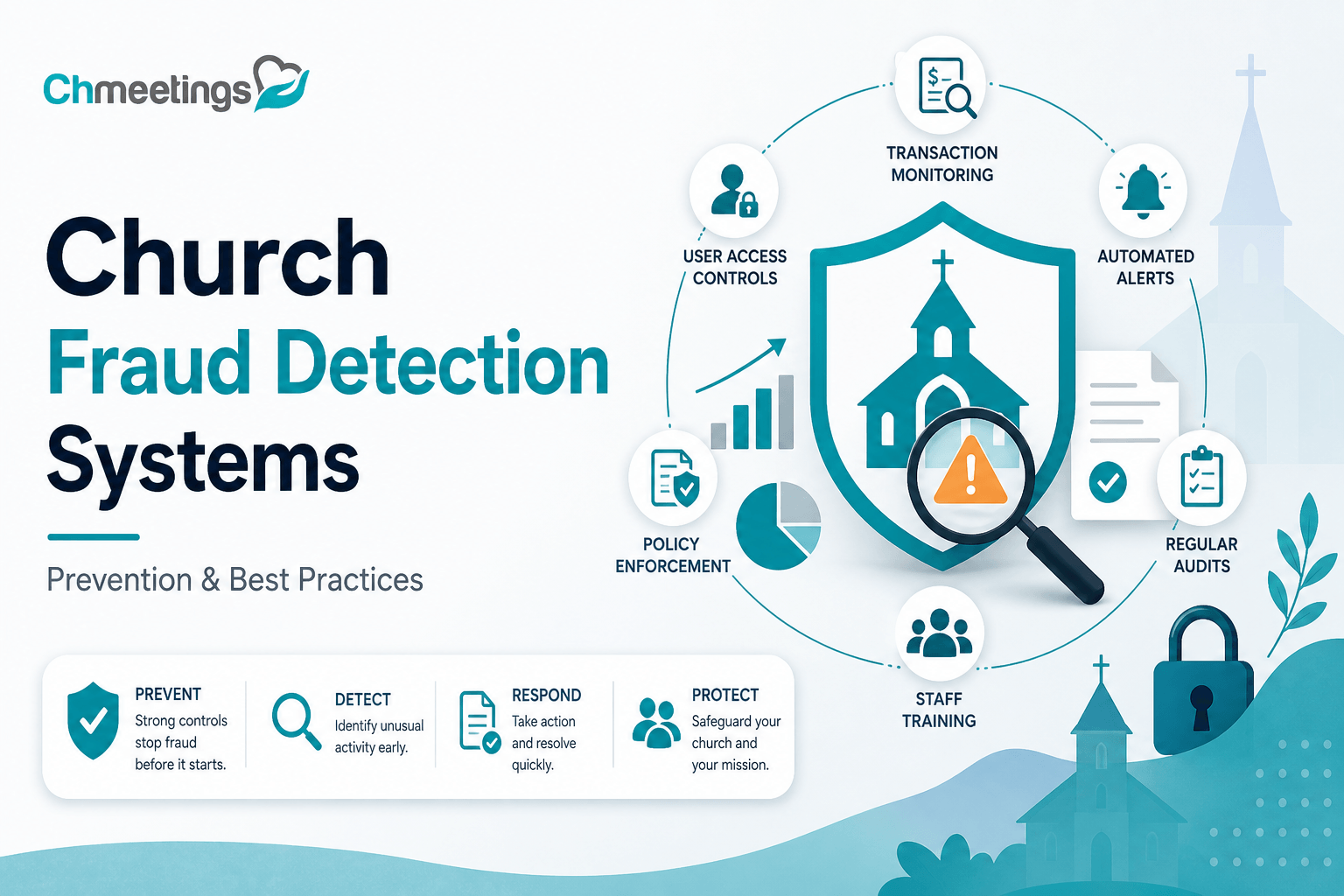
What Are Church Fraud Detection Systems?
Church fraud detection systems are tools and processes that help identify, flag, and investigate suspicious financial activity in a congregation. They combine automated monitoring, rule-based alerts, access controls, and reporting to protect donations, reimbursements, payroll, and vendor payments. For churches, which often rely on a mix of staff, volunteers, and cash, these systems turn manual guesswork into repeatable checks that protect ministry resources and donor trust.
Defining System Types And Purposes
- Rule-based transaction monitoring, which looks for specific behaviors like duplicate refunds, unusually large gifts, or back-to-back voids.
- Anomaly detection, which uses pattern recognition to surface transactions that don’t fit historical giving or expense patterns.
- Reconciliation and bank-feed tools, which compare giving and expense records to actual bank activity to find gaps and hidden accounts.
- Role and permission systems, which limit who can create, approve, or move funds and record those actions in an audit trail.
- Case management and incident logging, which track investigations, evidence, and outcomes so you can document responses and learn from them.
Each system type has a purpose: prevent diversion of funds, speed detection so issues are smaller and easier to fix, maintain clean records for auditors and donors, and protect volunteers and staff from false accusations by producing clear logs.
How Detection Fits Into Church Operations
Detection isn’t a separate project, it’s part of how you run the church’s finances. Practical places it belongs:
- Giving processing, where online and in-person donations are reconciled to bank deposits.
- Expense workflows, where approvals and receipts are required before payments happen.
- Volunteer roles, where access is limited and temporary permissions are tracked.
- Monthly close and reporting, where automated reconciliations reduce errors and uncover anomalies early.
Integrate detection into ordinary workflows so checks happen without extra busy work. Train the treasurer, finance team, and key volunteers on what alerts look like and who handles them. Make it part of staff onboarding and annual policy reviews. When prevention and detection live in your daily operations, your backend stays healthy, and ministry work faces fewer interruptions.
Assessing Your Church Fraud Risk
A clear risk assessment tells you where to focus limited resources. It starts by understanding what usually goes wrong, then identifying internal weaknesses and new risks created by digital giving.
Common Fraud Schemes In Churches
- Donation diversion, where cash or checks are pocketed before recording.
- Ghost donors, where someone fabricates gifts or inflates deposit totals to cover theft.
- Check tampering, altering payee or amounts after a check is written.
- Unauthorized refunds or duplicate refunds processed to a personal account.
- Fake vendor invoices, where someone creates shell vendors and pays themselves.
- Payroll or stipend fraud, adding ghost employees or inflating hours.
- Credit card or online payment abuse, using staff payment info for personal charges.
- Social engineering and phishing, tricking staff into sending funds or revealing credentials.
Knowing specific schemes helps you build targeted alerts and policies instead of generic fear-based controls.
Internal Risk Factors To Watch
- Weak segregation of duties, where one person can record, approve, and reconcile.
- Heavy reliance on cash or single-count controls for offerings.
- Manual spreadsheets and one-off processes that hide mistakes and fraud.
- High volunteer turnover, leaving gaps in knowledge or poorly monitored accounts.
- Lack of background checks for people in finance roles.
- No routine reconciliations between giving records, bank deposits, and accounting.
- Missing or infrequent audits and incomplete documentation for expenses.
Address these with simple, scalable steps: split duties, require receipts, automate reconciliations, and run periodic access reviews.
External Risk Factors From Digital Giving
- Payment account takeover, when donor or staff credentials are compromised.
- Fraudulent donations using stolen cards, then chargebacks that cost the church.
- Weak or poorly configured payment gateways, leaving APIs or webhooks open to manipulation.
- Third-party integrations that duplicate or mismatch transactions during sync.
- Phishing aimed at donors, asking them to reroute recurring gifts to fraudulent accounts.
Mitigate by choosing PCI-compliant payment processors, enabling multi-factor authentication, tokenizing payment methods, and reconciling online giving to bank feeds daily. Clear donor communications and secure member portals reduce the chance of social engineering.
Core Features Every Admin Needs
Detection features should make the finance team’s job easier, not slower. Focus on tools that give visibility, accountability, and reliable integration into your current systems.
Real Time Transaction Monitoring And Alerts
Real time monitoring catches problems before they compound. Key capabilities:
- Alerts for unusually large gifts compared to typical donor history.
- Notifications for duplicate transactions, rapid refund activity, or sudden spikes in new donors.
- Dashboard summaries that highlight trends, not just individual flags.
- Flexible rules so you can tune sensitivity without a developer.
When an alert appears, the system should give context, like donor history, linked bank deposits, and any related approval records, so the reviewer can act quickly.
Role Based Access And Audit Trails
Controls should limit risk and preserve accountability. Good features:
- Role based access, granting only the permissions needed for each person’s job.
- Time-limited or task-based permissions for volunteers handling special events.
- Immutable audit trails that record who did what, when, and from where.
- Exportable logs for audits or when you need to share evidence with leadership or authorities.
These features protect staff and volunteers by making actions transparent and reversible only through documented processes.
Seamless Integration With Giving And Accounting
Detection works best when it doesn’t live in a silo. Integrations that matter:
- Direct bank feed connections and automated reconciliation tools.
- Two-way syncing with your giving platform so gifts, refunds, and donor records stay aligned.
- Mapping to your general ledger or accounting system to avoid manual entries.
- Syncing with your church management app to keep member and giving profiles consistent.
A unified flow reduces human error and gives you faster, more accurate alerts. A church management app that centralizes people, giving, and reports makes detection scalable as your ministry grows.
Implementing Detection Technology
Buying software is only part of the solution. Implementation, tuning, and people processes determine whether detection prevents loss or just creates noise.
Selecting A Solution Checklist
Ask these questions before you buy:
- Does it match your size and budget, with clear pricing and trials?
- Is it PCI compliant and hosted securely?
- Does it support role based access, audit logs, and real time alerts?
- Can it integrate with your giving provider, bank feeds, and accounting?
- Is it easy for volunteers and staff to use without heavy IT support?
- Does the vendor offer support, training, and references from other churches?
- Can you export data and retain records for audits?
- Is the vendor’s roadmap aligned with your future needs?
Bring the pastor, treasurer, finance volunteers, and the person who runs your ChMS into the evaluation so you pick a practical fit.
Integrating With Your ChMS And Bank Feeds
Integration steps to reduce friction and errors:
- Map fields between systems, ensuring donor IDs, funds, and dates align.
- Set up automated bank feeds and test with a small sample before going live.
- Enable one-way or two-way sync depending on your workflow, but avoid duplicate writebacks.
- Use unique transaction IDs to prevent duplicates during imports.
- Schedule nightly reconciliations so discrepancies surface quickly.
- Train staff on how records flow and who owns each step.
Test thoroughly, document the process, and keep a rollback plan if a sync creates unexpected duplicates.
Setting Alert Thresholds And Workflows
Start conservative, then tune. Practical approach:
- Baseline your normal activity for 30 to 90 days, then set thresholds relative to those norms.
- Example triggers: single gift greater than 3 times the donor’s average, refund rate above 5% for a day, or more than three voids in 24 hours.
- Define a clear workflow for each alert level, who reviews it, and expected response times.
- Include steps for preserving evidence, freezing suspected funds if needed, and escalating to leadership or legal counsel.
- Track false positives and adjust rules monthly until alerts become meaningful and manageable.
Document the workflow in a short protocol so volunteers stepping in for finance know what to do. Over time, tuning reduces noise and makes your system a reliable early warning for problems.
Manual Controls That Prevent Loss
Strong manual controls reduce opportunity for theft and make problems visible early. These are low-tech, high-impact practices that work whether your finance team is paid staff or volunteers.
Segregation Of Duties And Dual Approvals
Split the key tasks so no one person can create, approve, and reconcile a transaction. Practical separations for small churches:
- One person records gifts and expenses, another approves payments, a third reconciles bank deposits.
- Require dual sign-off for checks or ACH payments above a dollar threshold set by leadership.
- Use time-limited permissions for event volunteers and document who has access and when.
Dual approvals protect everyone, and simple role matrices keep responsibilities clear without adding bureaucracy.
Cash Counting And Deposit Protocols
Cash is where churches are most vulnerable, so make counting and deposits predictable and verifiable.
- Always use at least two unrelated counters, with written count sheets signed by both.
- Count in a secure room with limited access, and store cash in tamper-evident bank deposit bags.
- Reconcile offering totals to bank deposits the same day or next business day, noting any variance and who handled funds.
- Use lockable drop boxes, sealed night deposits, or immediate bank deposits after larger events. Document each step so chain of custody is clear.
Vendor, Expense, And Check Controls
Control the payables process from vendor setup to final payment.
- Require vendor onboarding: W9 or equivalent, proof of services, and an approved purchase request before the first payment.
- Match invoices to purchase orders and receipts before issuing checks or ACH. No blank checks, ever.
- Limit check signers to two approved individuals and consider positive pay with your bank to stop altered checks.
- For expense reimbursements, require itemized receipts and supervisor sign-off, and reconcile reimbursements monthly to prevent duplicate claims.
Monitoring Digital Giving Securely
Digital giving scales ministry, but it also changes the threat landscape. Monitoring needs to be technical and routine.
Securing Online And Mobile Donations
Protect donor payment data and admin access.
- Use a PCI compliant payment processor and ensure your donation pages use SSL.
- Enable multi-factor authentication for finance and admin accounts, and limit who can issue refunds or edit donors.
- Tokenize card data so raw card numbers aren’t stored in spreadsheets or email.
- Keep donation forms and plugins updated, and vet any third-party integrations before connecting them to your systems.
Reconciling Donation Reports And Fees
Reconciling gives you a single source of truth for what donors intended and what actually hit the bank.
- Reconcile giving platform reports to bank deposits at least weekly, with daily checks during high-activity periods. Track gross gifts, processor fees, refunds, and net deposits.
- Match transaction IDs and timestamps so every gift links back to a donor record. Use your church management app, for example ChMeetings, to centralize donor profiles, mapped funds, and fee accounting for clean contribution statements.
- Track fee-bearing choices, like whether the church absorbed card fees or the donor covered them, and reflect that consistently in reports and statements.
Preventing Merchant Account And Refund Abuse
Refunds and merchant privileges are common attack vectors if left unchecked.
- Restrict refund capability to a small set of vetted staff, and require a documented reason and supervisor approval for every refund.
- Set refund and daily refund limits that trigger an alert and manual review when exceeded.
- Monitor chargeback rates and investigate spikes immediately, because chargebacks cost money and signal fraud.
- Keep email confirmations and donor receipts enabled so legitimate donors can spot unauthorized refunds and report them quickly.
Auditing And Reconciliation Routines
Regular reconciliations and audits are your financial pulse checks. Routines catch errors before they become crises.
Daily, Weekly, And Monthly Reconciliations
Define what gets checked and by whom at each cadence.
- Daily: verify batch totals, online gift receipts, and bank feed postings for the previous day. Flag missing deposits.
- Weekly: reconcile deposit detail to giving platform reports and clear any timing differences. Review outstanding refunds and voids.
- Monthly: reconcile bank statements to the general ledger, review payroll and benefit items, and investigate uncleared checks or stale items.
Assign sign-off responsibility and keep a short reconciliation checklist to ensure consistency.
Surprise Audits And Independent Reviews
Unannounced checks deter theft and reveal weak spots that routine reviews miss.
- Schedule random counts of offering receipts, surprise reconciliations, and spot checks of petty cash.
- Use an independent reviewer, like a trusted church member who is not in finance, or an outside accountant for periodic reviews.
- Rotate counters and reviewers so the same individuals are not always in control of cash-related tasks.
When To Engage Forensic Accounting
Call in specialists when evidence points beyond bookkeeping errors.
- Triggers include large unexplained variances, recurring reconciled discrepancies, repeated override of controls, or credible allegations.
- A forensic accountant preserves evidence, maps transaction timelines, and identifies intentional manipulation versus error.
- Expect to coordinate with leadership, legal counsel, and insurers, and to budget time and cost for a thorough review.
Investigating Suspected Misconduct
When suspicion arises, move carefully to protect evidence, people, and the church’s reputation.
Preserving Evidence And Chain Of Custody
Act fast to secure digital and physical evidence.
- Freeze affected accounts, preserve backups, and export logs and transaction histories immediately.
- Document who collected each item, when, and where it is stored. Sign and date evidence transfer forms.
- Avoid opening or altering files that may be needed for legal proceedings; imaging systems and exporting read-only copies is safer.
Conducting Interviews And Document Reviews
Investigations must be methodical and respectful.
- Use a neutral investigator if possible, and prepare interview questions tied to specific facts. Take written statements and get signatures when appropriate.
- Review emails, bank statements, internal notes, and reconciliation workpapers to build a timeline. Cross-check statements against documentary evidence.
- Keep interviews confidential and limit the circle of people who know details while the inquiry continues.
Partnering With Law Enforcement And Insurers
Know when to involve external authorities and how to work with them.
- Report suspected criminal activity to law enforcement when theft, forgery, or serious fraud is apparent, and share preserved evidence.
- Notify your insurance carrier early if you have employee dishonesty or loss coverage, and follow their claim procedures.
- Coordinate communications so legal counsel, law enforcement, and leadership are aligned, and include pastoral care for victims and shepherding for the congregation throughout the process.
Response Playbook And Templates
Incident Response Checklist
- Immediately secure accounts, change passwords for finance and admin logins, and enable multi-factor authentication where it’s not already on.
- Freeze suspect transactions and restrict refund/void privileges to a small, named group while you investigate.
- Preserve logs, bank statements, export transaction histories, and save copies in a read-only location to protect chain of custody.
- Assign roles, a single point of contact for leadership, and an investigation lead with a clear timeline for initial review within 24 to 72 hours.
- Conduct a quick reconciliation to quantify potential loss and identify the likely entry point, then document findings in a case file.
- If criminal activity is suspected, file a police report and notify your insurer promptly, following their claim instructions.
- Communicate limited, factual updates to key stakeholders as directed by leadership, and prepare a congregation message once facts are clear.
- After closure, capture lessons learned, update policies, adjust alert thresholds, and schedule retraining or access reviews.
Congregation Communication Templates
- Initial acknowledgement, short and calm: “We want you to know we detected irregular activity in our giving records. We’ve secured accounts and are investigating. No donor personal information has been shared. We’ll update you as facts emerge.”
- Follow up update, factual and respectful: “The finance team reviewed recent transactions and found X. We’ve engaged police/insurance/forensic accounting and frozen affected accounts. We’re reviewing internal controls and will share next steps this Sunday.”
- Recovery and restoration message: “The investigation is complete. Here’s what happened, what we recovered, and what we changed to prevent a repeat. If you have questions about your giving history, contact [finance email].”
- Donor action note, practical: “Please review your donation statements and bank activity for the past 90 days. If you see anything unexpected, contact us at [secure contact]. Consider changing passwords if you use the same login elsewhere.”
Tone rules: be transparent but factual, avoid naming or accusing individuals until findings are confirmed, offer a clear contact, and include pastoral care resources for affected members.
Insurance Claims And Recovery Steps
- Locate your fidelity/employee dishonesty, cyber, and crime policies, note reporting deadlines, and call your broker to confirm next steps.
- Prepare a claims packet: police report number, timeline, transaction logs, reconciliations, bank statements, and any forensic accountant summaries. Keep copies and a submission checklist.
- Follow insurer instructions on preserving evidence and allow them to advise on forensic steps they prefer. Delays or unilateral changes can harm coverage.
- Track recoverable amounts versus deductibles and document unrecoverable losses for donor and leadership transparency.
- Coordinate civil recovery only after law enforcement clears criminal proceedings, and consult legal counsel about restitution and subpoenas.
- After claim resolution, use findings to update controls, proof of loss templates, and your incident playbook so future responses are faster and cleaner.
Metrics To Track And Report
Key Performance Indicators To Monitor
- Time to detect, measured from suspicious transaction to first alert. Shorter is better.
- Time to respond, from alert to containment action. Target same day for high-risk alerts, 72 hours for lower risk.
- Number of alerts versus number of confirmed issues, to track false positive rate.
- Reconciliation lag, days between donation and bank reconciliation. Aim for daily or weekly depending on volume.
- Refund and chargeback rate, by day and by event. Spikes need immediate review.
- Percentage of high-value transactions manually reviewed, and percent of transactions with dual approvals.
- Audit exceptions and unresolved reconciling items older than 30 days.
These KPIs help leadership see program health, justify automation, and prioritize controls.
Building A Fraud Monitoring Dashboard
- Include panels for real-time alerts, time to detect/resolve averages, reconciliation status, refund/void trends, and top flagged donors or vendors.
- Use color coding for severity, and allow one-click drilldowns to the supporting transaction, receipts, and audit logs.
- Refresh frequency should match your volume, daily for most churches, real-time for higher volume ministries.
- Limit visibility based on role, so volunteers see what they need and finance leaders see escalations.
- Host the dashboard within your church management app or a secure BI tool to keep people and giving data aligned, avoiding manual exports that introduce error.
- Keep the layout simple, mobile-friendly, and focused on actions, not just numbers.
Using Trend Analysis To Improve Detection
- Baseline normal giving behavior by season, by fund, and by donor cohort so alerts are relative, not absolute.
- Watch moving averages and month-over-month changes to catch slow diversions that single-transaction rules miss.
- Track refunds, voids, and exception counts after special events, since one-off collections often create anomalies.
- Use trend reports to justify threshold changes and to test whether tuning reduces false positives without missing real issues.
- Review trends quarterly with leadership so detection evolves with ministry programs and new giving channels.
Comparing Detection Approaches
In House Versus SaaS Solutions
- In-house gives control and customization, but it needs technical skill, maintenance, secure hosting, and ongoing patching that small teams often can’t sustain.
- SaaS offers built-in security, automatic updates, and vendor support, which keeps the burden off volunteers and scales with growth.
- Consider total cost of ownership, not just licensing, include backups, staff hours, and compliance work.
- For most small to mid-sized churches, SaaS is a practical choice because it shifts risk and maintenance to specialists, freeing leaders to focus on ministry.
Rule Based Versus Machine Learning Models
- Rule-based systems are transparent, easy to explain to volunteers, and quick to implement for known fraud patterns. They’re good for simple, high-value checks.
- Machine learning can surface subtle anomalies and adapt as donor behavior changes, but it needs data, tuning, and sometimes vendor expertise to interpret results.
- A hybrid approach often works best, start with rules for core checks, add anomaly detection for complex patterns as your data volume grows.
Cost, Scalability, And Support Tradeoffs
- Cheaper options usually mean more manual work and risk of missed issues as volume grows. Higher-cost vendors add automation, support, and compliance features.
- Scalability matters: choose solutions that let you add users and sites without redoing architecture or retraining volunteers from scratch.
- Evaluate vendor support SLAs, training resources, and community references, because good support shortens incident response and reduces volunteer burnout.
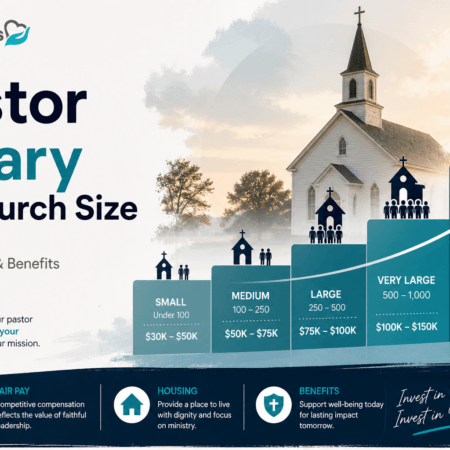
Practical Guide For Small Churches
Low Cost Tools And Workarounds
- Use bank alerts, email rules, and scheduled exports to create a lightweight monitoring loop without new software.
- Template spreadsheets with unique transaction IDs, automated sum checks, and simple pivot reports catch many errors.
- Free or low-cost MFA apps, password managers, and bank positive pay services dramatically reduce common attack surfaces.
- Leverage volunteers with bookkeeping experience and run frequent, short reconciliations after big events to avoid month-long drifting.
Simple Controls For Volunteer Run Teams
- Keep roles clear, document who can do what, and rotate cash counters and reviewers to avoid concentration of opportunity.
- Require dual signoffs for deposits and for payments above a small threshold your leadership sets.
- Use short SOP checklists for counting, depositing, and reconciling so substitutes can step in without mistakes.
- Revoke access when volunteers leave, and avoid shared credentials by using role accounts or a password manager with audit logs.
Knowing When To Outsource Financials
- Consider outsourcing when you face repeated reconciliation errors, no reliable volunteer pool, payroll complexity, or when donor size and volume grow faster than your controls.
- Outsourcing options include part-time bookkeepers, a church-focused accounting firm, or managed giving services that handle deposits and reconciliations.
- Weigh costs against the value of faster detection, stronger controls, and the time it frees leaders to focus on ministry.
- Start with a trial period, clear deliverables, and a short transition checklist so responsibilities and reporting lines are tidy from day one.
Building A Prevention Culture
Prevention starts with people, not just software. When your leadership, staff, and volunteers expect controls and know why they exist, fraud becomes much harder to hide.
Training Staff And Volunteers Regularly
Training should be short, practical, and repeated. Cover common schemes, how to spot suspicious transactions, your approval workflows, and how to preserve evidence. Use real examples from church settings, run short tabletop exercises after big events, and require a quick refresher whenever a finance role changes. Make training accessible, recordable, and part of onboarding so new volunteers know the rules from day one.
Background Checks And Role Assignment
Screening should match the role’s risk. For those handling cash, checks, or refunds, a basic background check and reference call is reasonable. Assign roles by the principle of least privilege, so people only get the access they need. Rotate counters and reviewers periodically, lock out accounts when someone leaves, and run quarterly access reviews so permissions don’t drift.
Encouraging Reporting And Transparency
Create clear, safe ways to report concerns, including an anonymous channel for volunteers who fear retaliation. Publish a short reporting policy that explains who reviews complaints and expected timelines. Protect confidentiality, offer pastoral care to affected people, and commit to factual updates for leadership and the congregation. When you handle reports promptly and fairly, donors and volunteers trust your stewardship more.
Common Implementation Mistakes
Even well-intended churches stumble when rolling out detection systems. Avoid these common missteps.
Overreliance On Technology Alone
Software flags problems, it doesn’t fix culture or sloppy processes. Alerts without clear human workflows create noise and fatigue. Combine tools with written procedures, trained reviewers, and routine reconciliations. Treat technology as an amplifier of good controls, not a replacement.
Loose Approvals And Missing Reconcilations
Giving one person the power to create, approve, and reconcile payments is risk in plain sight. Missing or infrequent reconciliations let small gaps grow into major losses. Require dual approvals for thresholds set by leadership, document approval chains, and reconcile deposits and expenses on a defined cadence so exceptions appear quickly.
Ignoring Small Red Flags Early
A few odd transactions today rarely mean nothing tomorrow. Small red flags include repeated small refunds, new vendors with PO boxes, duplicate invoice numbers, or daily deposits that don’t match batch totals. Investigate anomalies promptly, log near-misses, and tune rules so patterns get noticed before they escalate.
FAQs
How Do Church Fraud Detection Systems Work?
They combine automated checks with human review. Systems ingest giving and bank feeds, apply rules and anomaly detection, and surface alerts with supporting documents. Reviewers follow predefined workflows to investigate, preserve evidence, and escalate. The blend of real-time alerts, reconciliation, role controls, and audit trails is what makes detection practical for churches.
What Are The Red Flags Of Embezzlement?
Look for unexplained variances between batch totals and deposits, missing or altered receipts, duplicate or altered vendor invoices, unusual refunds or voids, frequent reconciliations that never balance, and resistance to access removal or process changes. Sudden lifestyle changes or secrecy around financial tasks may accompany transactional signs.
Can A Small Church Afford Detection Tools?
Yes. Start with low-cost controls: bank alerts, daily export checks, simple rule-based spreadsheets, and routine reconciliations. Many vendors offer tiered pricing or free plans for small groups. The cost of basic prevention is usually far less than a single theft. If volume grows, introduce paid tools that automate reconciliation and alerting to save volunteer hours.
When Should We Call Law Enforcement?
Call law enforcement when there is credible evidence of theft, forgery, or criminal intent, especially if the suspect has access to records that could be destroyed. If you’re unsure, preserve evidence, consult legal counsel or your insurer, and then involve police. Early reporting protects evidence and avoids claims failures later.
What Metrics Show Detection Effectiveness?
Track time to detect, time to respond, reconciliation lag, false positive rate, refund and chargeback trends, percentage of transactions with dual approvals, and unresolved audit exceptions over 30 days. Those numbers tell leadership whether controls are working or just producing noise.
Which Systems Integrate With My ChMS?
Look for systems that support bank feeds, payment processor syncs, two-way giving updates, accounting exports, and single sign-on or API connectivity. Test integrations in a sandbox to check transaction IDs, fund mapping, and duplicate prevention. Integration quality matters more than brand, because clean data reduces false alerts and reconciliation work.
How Long Does Investigation Usually Take?
It depends on scope. Simple reconciliations or paperwork mismatches can be cleared in a few days. Internal investigations with interviews and document review often take one to four weeks. Forensic accounting or criminal probes can stretch to several months. Timely evidence preservation and clear scope speed things up.
Does Insurance Cover Employee Theft?
Many churches carry fidelity or employee dishonesty coverage and cyber or crime policies that may cover theft, but coverage varies. Notify your insurer immediately, follow their evidence preservation instructions, and provide a claims packet with timelines, transaction logs, and police reports if filed. Read policy limits and deductibles so leadership knows recovery expectations.